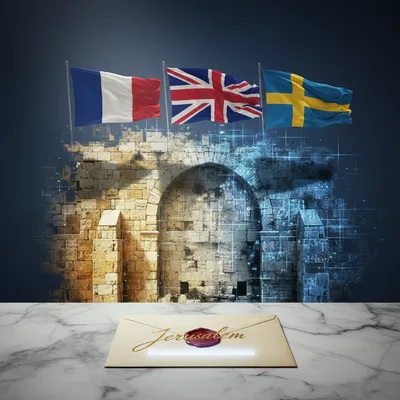
Imagine you are a Mossad analyst sitting in an office in Tel Aviv. You are monitoring a high-priority target, maybe a mid-level coordinator for a proxy group, and you intercept a fragment of a conversation. It is specific. It is actionable. There is a plan to hit a high-profile Israeli target in Berlin, and it is happening in forty-eight hours. Now, here is the problem: you have no legal authority to kick down a door in Germany. You can’t make an arrest, and if you send a team in to handle it quietly, you risk a massive international incident with a key ally. So, what do you do? Today’s prompt from Daniel is about exactly that. He wants us to dig into the mechanics of bespoke intelligence sharing, specifically how agencies like Mossad coordinate with European law enforcement and how they plug into larger networks like the Five Eyes.

It is a fascinating world because it sits right at the intersection of high-stakes espionage and standard police work. And by the way, just a quick note for the listeners, today’s episode is powered by Google Gemini Three Flash. But getting back to the scenario you laid out, Corn, that handoff between a foreign intelligence agency and domestic police is what we call bespoke intelligence sharing. It is not like the movies where the spy just does everything. In the real world, the spy provides the lead, but the local cop provides the handcuffs.

It sounds like a delicate dance. You have two organizations with completely different cultures, different legal frameworks, and frankly, different goals. One wants to protect national security at all costs, and the other has to worry about things like the chain of evidence and the right to a fair trial. How do they actually pass that folder across the table without the whole thing falling apart in court?

That is the million-dollar question. I am Herman Poppleberry, and I have been looking into the technical pipeline of how this information travels. It is often described as the intelligence-to-evidence pipeline. You see, Mossad or the CIA might have a piece of information that is incredibly "hot," meaning it came from a sensitive source, like a bugged room or a deep-cover human asset. They cannot just hand that recording over to the German Federal Police, the BKA, and say, "Here, play this for the judge." If they did, they would burn their source and lose that window into the enemy forever.

So they have to "launder" the intelligence? That sounds a bit shady, but I assume there is a formal process for it.

Laundering is a cynical way to put it, but technically, they call it sanitization. The intelligence agency provides what is called "lead information." They tell the local police, "We have high confidence that a cell is operating out of this specific apartment in the Neukolln district of Berlin." They don't tell them how they know; they just tell them where to look. Then, the local police have to go out and "re-discover" that same information using their own legal tools. They set up their own surveillance, they get their own warrants, and they build a parallel case that can actually stand up in a European court of law.

But wait, how does that work in practice if the clock is ticking? You mentioned forty-eight hours in your intro. If the BKA has to start from scratch—setting up their own wiretaps and tailing suspects—doesn't that eat up the very time they need to prevent the attack?

That’s where the "bespoke" part gets really intense. In a high-speed scenario, the local police might use the foreign intelligence to justify an "emergency" surveillance order. They aren't starting from a blank map; they are starting with a cheat sheet. They know exactly which burner phone to target or which car to put a tracker on. They are still doing the work, but they are doing it with the "answer key" in their pocket. It’s about creating a domestic paper trail that mirrors the intelligence without referencing the intelligence.

It seems like a lot of extra steps, but I guess that is the price of living in a rule-of-law society. If you just arrested people based on a "tip" from a foreign spy agency without any corroborating domestic evidence, the defense lawyers would have a field day. But why is this relationship so "bespoke," as Daniel put it? Why isn't there just a giant database where all these countries share everything automatically?

Because intelligence is the ultimate currency, Corn. You don't just give away your best assets for free. The Five Eyes, which is the United States, United Kingdom, Canada, Australia, and New Zealand, is the closest thing we have to a "giant database," but even that is restricted to the inner circle. For everyone else, including a powerhouse like Israel, the sharing is event-driven and transactional. It is a "you scratch my back, I'll scratch yours" arrangement. Israel has deep linguistic and cultural penetration into Middle Eastern networks that European agencies simply cannot match. In exchange for that "ground truth," Europe provides the diplomatic and operational cooperation that Israel needs to keep its citizens safe abroad.

So it is a marketplace. Mossad is selling high-grade leads, and the Europeans are paying in sovereignty and cooperation. I want to get into the nuts and bolts of how they actually talk to each other. Is there a secure Slack channel for spies? How does a Mossad analyst actually get a message to a detective in Berlin or Copenhagen?

It usually goes through the "Legal Attache" or a dedicated liaison officer. Most major Israeli embassies in Europe have a Mossad liaison. Their entire job is to sit in a room with their counterparts from the local domestic security service, like Germany’s BfV or France’s DGSI. They build personal trust over years. When that "hot" lead comes in from Tel Aviv, the liaison officer literally walks over or uses a dedicated, air-gapped terminal to pass the sanitized packet.

Does that mean the quality of the intelligence sharing depends on the personal relationship between two individuals? That sounds like a single point of failure. What if the Mossad guy and the French guy just don't get along?

It’s more common than you’d think. There’s a famous story—though names are always redacted—of a liaison relationship in a Southern European capital that completely stalled because of a disagreement over a shared informant. The flow of data slowed to a trickle until one of the officers was rotated out. This is why agencies invest so much in "liaison diplomacy." They host dinners, they share training exercises, they essentially build a sub-culture of trust that exists outside of their respective governments' official stances. They need that "social capital" for when the forty-eight-hour clock starts ticking.

You mentioned Germany specifically. I remember reading about a plot against a synagogue in Berlin back in twenty-twenty-three. Was that one of these bespoke handoffs?

It was a textbook example. In December of twenty-twenty-three, German authorities arrested several individuals linked to Hamas who were allegedly planning attacks on Jewish institutions. The reports later confirmed that the initial "tip" came from Israeli intelligence. Mossad had intercepted communications showing that these individuals were receiving orders from Hamas leadership in Lebanon. But again, Mossad didn't do the raid. They gave the BKA the "who" and the "where," and the German police spent weeks doing their own legwork to ensure the arrests would stick.

It is interesting that you mention the Hamas leadership in Lebanon. That implies a level of signals intelligence, or SIGINT, that goes beyond just having a guy on the street. This brings us to the second part of Daniel’s prompt: the Five Eyes and those broader networks. How does a non-member like Israel interact with a club that exclusive?

This is where it gets really technical and, frankly, a bit murky. Even though Israel isn't one of the five formal members, they are what is known as a "Tier Three" or a "Tier B" partner. They aren't in the room when the five big bosses are talking, but they have specialized Memorandums of Understanding with the NSA and the GCHQ. There was a famous leak years ago that suggested the NSA actually shares raw, unmined SIGINT data with Israel. That is almost unheard of for a non-ally. Usually, you only share the "finished" reports. Sharing the raw data means you trust the other side's analysts as much as your own.

That is a huge level of trust. Why would the U.S. give raw data to Israel? What is the return on investment there?

Geography and expertise. The U.S. has the biggest vacuum cleaner in the world when it comes to data, but they don't always have the best filters. Israel has some of the best Arabic and Farsi linguists on the planet, and they have a geographic proximity that gives them a different perspective. If the NSA picks up a massive amount of encrypted traffic coming out of Iran, they might pass a chunk of it to Israel and say, "See if you can find the signal in this noise." Israel gets the data, and the U.S. gets the high-level analysis.

So it’s like outsourcing the homework to the smartest kid in the class. But how does that data then get to the European police? If the NSA gives data to Mossad, and Mossad finds a plot in Berlin, can Mossad just give that U.S.-sourced data to the Germans?

No, and that is a massive rule in the intelligence world called the "Third Party Rule." If Agency A gives something to Agency B, Agency B cannot give it to Agency C without explicit permission. This is what keeps the "bespoke" nature of the trust alive. If Mossad burned a U.S. source by giving it to the Germans without asking, the U.S. would cut them off tomorrow. So, there is this incredible bureaucratic layer where the liaison officers have to clear every single piece of data for "downstream sharing."

But isn't that incredibly slow? If Mossad sees an imminent threat in London using NSA data, do they really have to call Maryland first to ask if they can tell the Brits?

In theory, yes. In practice, there are "pre-approved" categories. For "Life and Limb" situations—meaning an immediate threat of death—most of these agreements have an "emergency bypass" clause. You share first and apologize later. But you better be right. If you use the emergency bypass for something that wasn't actually an emergency, you lose your privileges. It’s a system built on the concept of "proportionality."

It sounds like a nightmare of paperwork. But I suppose when lives are on the line, people find a way to move fast. I’m thinking about the "Hamas Octopus" investigation you mentioned earlier. That wasn’t just one country; that was Denmark, Germany, and the Netherlands all acting at once. How do you coordinate a multi-country raid based on one agency’s intelligence?

That was a massive operation in late twenty-twenty-three and early twenty-twenty-four. Mossad provided evidence of a coordinated Hamas network across Europe that was actually looking for buried weapons caches. Think about that for a second. This wasn't just "chatter"; this was operational logistics. Because it involved multiple European countries, the sharing had to go through Europol and specialized counter-terrorism task forces like the Counter Terrorism Group, or CTG, which is an informal forum for the heads of European security services. It shows that the "bespoke" model is evolving. It is becoming more of a hub-and-spoke system where Israel provides the "hub" intelligence, and the European "spokes" execute the mission.

Let’s pause on that "buried weapons" detail. That sounds like something out of a Cold War thriller. Are we talking about actual crates of guns in the woods?

We’re talking about pre-positioned caches. The intelligence suggested that these cells weren't trying to smuggle guns across borders in twenty-twenty-four; they were looking for stuff that had been stashed years ago, or they were being told where to find "dead drops" managed by third-party criminal organizations. This is why the sharing is so vital. A Danish policeman might see a guy digging in a park and think it’s a local crime or a mental health issue. But when Mossad provides the context that this specific park was a known drop point for a specific cell, that local incident suddenly becomes a high-priority national security case.

It’s wild to think about Hamas operatives looking for buried weapons in a park in Denmark or a forest in Germany. It sounds like a spy novel, but these are real arrests. What I find curious is the political friction. We know that European governments and Israel don't always see eye-to-eye on policy, especially lately. Does the intelligence sharing stop when the politicians start arguing?

Almost never. That is one of the "dirty secrets" of the intelligence world. The "spooks" usually have a much better relationship than the "suits." Even when a European capital is publicly criticizing Israeli military actions, their intelligence services are still on the phone with Mossad every single day. Why? Because the threat of a terror attack on European soil is a political death sentence for a domestic government. They cannot afford to turn away high-quality intelligence just because they disagree with a country's foreign policy. Intelligence is the ultimate pragmatic bridge.

But does that ever lead to a "quid pro quo" that gets uncomfortable? Like, "We'll give you this tip on a bomber in Paris, but you need to go easy on us in the next EU vote"?

It’s rarely that explicit. It’s more about "institutional goodwill." If Mossad keeps the streets of Paris safe, the French intelligence service becomes a powerful internal lobby for maintaining a working relationship with Israel, even when the French Foreign Ministry is furious. It’s about creating "necessary allies" within the government apparatus.

It’s like a separate layer of reality. You have the public diplomatic layer where everyone is posturing, and then the basement layer where everyone is trading secrets to keep the lights on. Let’s talk about the technical side of the Five Eyes again. You mentioned something called "Stone Ghost." What is that?

Stone Ghost is the name of the actual secure network used by the Five Eyes to share information. It is a highly encrypted, closed-loop system. It’s not just an email server; it’s a completely separate infrastructure. Most countries would give anything for a terminal on Stone Ghost. Israel doesn't have a terminal, but they have what are essentially "drop boxes." When there is an active threat, the Five Eyes can "downgrade" a packet of information from Stone Ghost—meaning they strip out the most sensitive source-identifying markers—and move it into a channel that Israel can access.

"Downgrading" sounds like taking a high-res photo and turning it into a blurry thumbnail so you can send it over a slow connection.

That’s a decent way to visualize it, but it’s more about the metadata. If a SIGINT satellite picks up a phone call, the "high-res" version includes the exact satellite coordinates, the frequency used, and the specific intercept method. The "downgraded" version just includes the transcript of the call and the identity of the speakers. You give the partner the "what," but you protect the "how." If Israel knows exactly which satellite caught the call, they could theoretically reverse-engineer the U.S. satellite’s orbit and capabilities. No one wants that.

And I assume Israel does the same thing in reverse? They aren't going to tell the BKA exactly which apartment in Beirut they have bugged.

Precisely. It is all about protecting the "sources and methods." If the BKA knows exactly how Mossad got the info, there is a risk that a leak in the German police force could get back to the targets. And we have seen that happen. There have been cases where European police services were infiltrated by radical sympathizers or even foreign agents from places like Iran or Russia. That is why the "bespoke" nature is so important. You only give what is absolutely necessary for the task at hand. It's the "need to know" principle applied at a continental scale.

I want to dig into that infiltration point. If a European agency is "leaky," does Mossad stop sharing with them? How do they handle a partner they don't fully trust?

They use what’s called "compartmentalization." They might share the lead with a very specific, vetted unit within the police—like the GSG 9 in Germany or the RAID in France—rather than the general force. They bypass the standard hierarchy and go straight to the "operators" who they know have been vetted to a higher standard. This creates its own friction, obviously, because the police chiefs don't like being bypassed, but it’s the only way to ensure the intelligence doesn't walk out the back door.

It feels like there is a lot of "trust but verify" going on. I’m curious about the cyber side of this. We’ve been talking a lot about terror plots and physical attacks, but what about state-level threats? We’ve seen reports of Iranian cyber-espionage targeting European infrastructure. Is the sharing mechanism the same for that?

It is similar, but the players change slightly. Instead of just the police, you bring in the national cyber security centers—like the NCSC in the UK or the BSI in Germany. Israel is a cyber superpower, and they are often the first to see new Iranian malware or "zero-day" exploits because they are on the front lines of that digital war every day. In twenty-twenty-four, there was a major case in Munich involving cyber-espionage where Five Eyes provided the initial signals intelligence—the "digital fingerprint" of the hack—but Mossad provided the "HUMINT" context—the human intelligence—that explained what the Iranians were actually looking for. It turned out they were targeting aerospace components related to satellite technology.

That is the perfect example of the synergy. The Five Eyes "sees" the data moving, but Mossad "understands" the intent because they have assets who know the people involved. It is a multi-layered puzzle. How do they reconcile the different definitions of "threat"? What if Israel thinks a certain group is a terror organization, but a European country sees them as a legitimate political movement?

That is the biggest hurdle in bespoke sharing. Take Hezbollah, for example. For a long time, many European countries distinguished between the "political wing" and the "military wing" of Hezbollah. Israel, obviously, makes no such distinction. If Mossad passed a tip about a "political" fundraiser that was actually a logistics meet, the Europeans might have been legally unable to act on it. Over the last decade, however, you’ve seen a massive shift. Germany, the UK, and others have moved to ban the organization in its entirety. That shift wasn't just a political choice; it was driven by years of Mossad providing "bespoke" evidence showing that the two wings were functionally identical. The intelligence actually drove the policy change.

I want to shift gears a bit and talk about the second-order effects. If these agencies are sharing so much information informally, does that undermine the official treaties? Does it make the formal alliances less relevant if you can just get what you need through a "bespoke" handoff?

I think it actually strengthens them by creating a "buffer." Formal treaties are rigid. They require parliamentary approval, they are subject to public scrutiny, and they are hard to change. Bespoke sharing is flexible. It allows countries to cooperate on specific threats without having to sign up for each other's entire worldviews. It allows Germany to work with Israel on counter-terrorism while still maintaining a different stance on Middle Eastern geopolitics. It is the "safety valve" of international relations. It allows the machine to keep working even when the operators are shouting at each other.

But what does this mean for the average person? If the line between "intelligence" and "law enforcement" is blurring, does that mean our data is being traded around more than we realize? If I’m a traveler in Europe, is my metadata part of this "bespoke" marketplace?

That is the thorny part of the privacy debate. When information is shared "ad-hoc," there is often less oversight than there is with formal, treaty-based sharing. In a formal system, you have data-protection ombudsmen and clear rules about how long data can be kept. In a bespoke handoff, the rules are often set by the "Memorandum of Understanding" between the two specific agencies, which is almost always classified. So, yes, there is a transparency gap. If your data is caught up in a sweep because you happened to be staying in the same hotel as a target, you might never know that your profile was shared between three different national agencies.

It’s the classic trade-off: security vs. privacy. Most people are happy that the synagogue plot was foiled, and they probably don't care that a Mossad analyst saw a packet of metadata to make it happen. But when you scale that up to a global level, it starts to feel a bit like a "shadow" legal system.

It is a shadow system, but it’s one born out of necessity. The threats are global, but the laws are still national. Until we have a "world police force"—which nobody actually wants—the only way to stop a target in Berlin based on a phone call in Beirut is through these informal bridges. What I find wild is how much this relies on individual relationships. You might have a Mossad liaison in Paris who is a legend, and because the French trust him personally, the sharing is seamless. If he gets replaced by someone they don't like, the intelligence flow can literally dry up for a few months.

That is terrifying. The safety of millions of people depends on whether two guys in a basement in Paris get along?

To a certain extent, yes. Intelligence is a human business. Even the most advanced SIGINT from the Five Eyes eventually has to be interpreted by a human and handed to another human who has to decide whether to act on it. You can have the best satellite in the world, but if the guy receiving the data doesn't trust the guy sending it, he might just file it away as "unreliable."

Let's talk about the future of this. Daniel mentioned the surging threats since October seventh, twenty-twenty-three. How has that changed the "marketplace"? Is Israel giving away more for free now to build goodwill, or are they being more selective because they are so stretched thin at home?

It’s both. On one hand, Mossad is more focused on domestic threats than ever before. But on the other hand, the global "Hamas network" has become a much higher priority for European services who previously saw it as a "Middle East problem." Now they see it as a domestic security problem. So, the demand for Israeli intelligence has skyrocketed. Israel is using this as a form of "intelligence diplomacy." By saving lives in Europe, they are creating a "debt of gratitude" that pays off in the diplomatic arena.

Can you give an example of how that "debt" is called in?

It’s usually seen in what doesn't happen. Maybe a European country decides not to support a specific sanctions package, or they choose to abstain from a vote rather than voting against Israel. It’s also seen in "legal cover." If Israel needs to conduct a sensitive operation on European soil—not a hit, but maybe a high-stakes surveillance op—a "grateful" local service might be more inclined to look the other way or provide logistical support that they wouldn't offer to a stranger.

"Intelligence as a currency." It’s a cold way to look at it, but it makes sense. If you save a city from a major attack, it’s a lot harder for that country’s leader to completely snub you at the United Nations the next week.

And it’s not just about terror. It’s about "hybrid threats." We are seeing more and more crossover between organized crime and state-sponsored terrorism. In twenty-twenty-four, there were reports of Iranian-backed criminal gangs in Sweden targeting Israeli interests. Now, the Swedish police aren't experts on the Iranian Revolutionary Guard, so they have to lean on Mossad. In return, Mossad gets access to Swedish police databases on these criminal networks. It’s an expansion of the "bespoke" model into areas we wouldn't normally think of as "spy stuff."

It’s like a merger between the FBI and the CIA, but on a global scale. I’m thinking about the practical takeaways for our listeners. If you are a security professional or even just a frequent traveler, what does this world of "bespoke sharing" mean for you?

First, it means that the "official" travel advisories from your government are only the tip of the iceberg. Those advisories are often based on this secret intelligence sharing. If the State Department suddenly raises the threat level for a specific European city, there is a very good chance it’s because of a "bespoke" tip that hasn't been made public yet. So, take those advisories seriously.

And for the professionals?

For anyone in the corporate security or cybersecurity world, the takeaway is that "relationships are data." You can have the best threat-intelligence feed in the world, but the most valuable information is often what isn't in the feed. It’s what is being shared through informal networks. If you aren't building relationships with your counterparts in other sectors or even other countries, you are missing the most critical "lead information." You need to be part of the "bespoke" conversation.

It also strikes me that we should be looking at declassified reports from agencies like the BKA or the Danish PET. They don't give away the secrets, but they often publish "annual reviews" that hint at these sharing patterns. If you read between the lines, you can see which way the "intelligence wind" is blowing.

You definitely can. For instance, if you see a sudden spike in arrests for "logistical support" in a country like Denmark, and the report mentions "international partners," you can bet your bottom dollar that was a bespoke handoff from an agency with a deep reach into the Middle East. You can actually track the geopolitical shifts by looking at the "thank yous" in these police reports.

This has been a deep dive, Herman. We've gone from the "Stone Ghost" network of the Five Eyes all the way down to buried weapons in a public park. It really paints a picture of a world that is much more interconnected—and much more fragile—than most people realize.

It is fragile because it depends on trust, and trust is hard to build but easy to break. But for now, this "bespoke" system is the only thing keeping the "Hamas Octopus" or Iranian proxies from having a free hand in Europe. It’s a fascinating, messy, and absolutely essential piece of global security.

I’m left wondering how AI is going to change this. If we start having AI-driven intelligence analysis, does the "human trust" element become less important? Or does it become even more critical because we need a human to verify what the machine is telling us?

I think it becomes more critical. You might have an AI that can scan the entire Five Eyes SIGINT flow in seconds, but you still need a human liaison to look his counterpart in the eye and say, "This is real. You need to move now." You can't put a machine's reputation on the line. If an AI makes a mistake and causes a false arrest, who do you blame? But if a liaison officer stakes his reputation on a lead, that means something.

That is a great point. The "liaison" isn't just a messenger; they are a guarantor. They are saying, "My agency stands behind this data."

And that is something a "shadow legal system" can't function without. It requires a face and a name.

Well, I think we've covered the "what," the "how," and the "why" of Daniel's prompt. It’s a wild world out there, and I’m glad we have people like Herman to help us navigate the technical side of it.

And I’m glad we have Corn to keep me from getting too lost in the "Stone Ghost" terminals.

Someone has to keep us grounded. Before we wrap up, I want to say thanks to our producer, Hilbert Flumingtop, for keeping the gears turning behind the scenes.

And a big thanks to Modal for providing the GPU credits that power the AI systems we use to research and produce this show. It’s pretty cool that we can use these tools to talk about the very world they are helping to shape.

This has been My Weird Prompts. If you enjoyed this deep dive into the world of "bespoke" spies and secret handoffs, do us a favor and leave a review on your favorite podcast app. It really does help other curious minds find the show.

We’ll be back next time with whatever weirdness Daniel sends our way. Until then, stay curious.

And keep your eyes open. You never know what's being "sanitized" for your protection.

Goodbye, everyone.

Catch you on the next one.